More open source, more security problems
The amount of open source code actively used in production for modern software applications across different industries has exploded in recent years. Using open source software has become the de-facto standard for modern software development. Over 72% of respondents in a recent Linux Foundation report of FOSS usage at Financial Services companies reported that they commit to looking for open source solutions before proprietary ones.
The usage of FOSS has many advantages, but it also comes with security concerns, especially for software vulnerabilities. “Using Components with Known Vulnerabilities” is one of the OWASP Top 10 Most Critical Web Application Security Risks. It is important to note that there is no evidence that open source software is more vulnerable than proprietary software.
Current comprehensive databases of known FOSS software vulnerabilities are predominately proprietary and privately maintained. Identifying vulnerable components in these systems is hindered by data structures and tools that are:
- Designed for proprietary software components
- Not comprehensive or complete
- Too dependent on voluntary submissions to the National Vulnerability Database.
These should be open data and FOSS tools – open source for open source.
We see our customers struggling to find a way to integrate software vulnerability identification into their CI/CD workflows without the high cost and complexity of proprietary tools. The explosion of FOSS usage across industries requires a new approach to efficiently identify FOSS security vulnerabilities, one based on open data and FOSS tools.
VulnerableCode is a new solution that uses FOSS tools to find FOSS software vulnerabilities and improve FOSS security. By collecting and parsing data from many sources, identifying packages using a standardized package url, and providing the data through a REST API, VulnerableCode addresses key security concerns for using FOSS code in modern applications.
The benefit: improved security of software applications with open data and tools for everyone.
A FOSS tool to find FOSS vulnerabilities
With VulnerableCode, we are building FOSS tools to aggregate, correlate, and curate software component vulnerability data from multiple sources and automate the search for FOSS component security vulnerabilities.
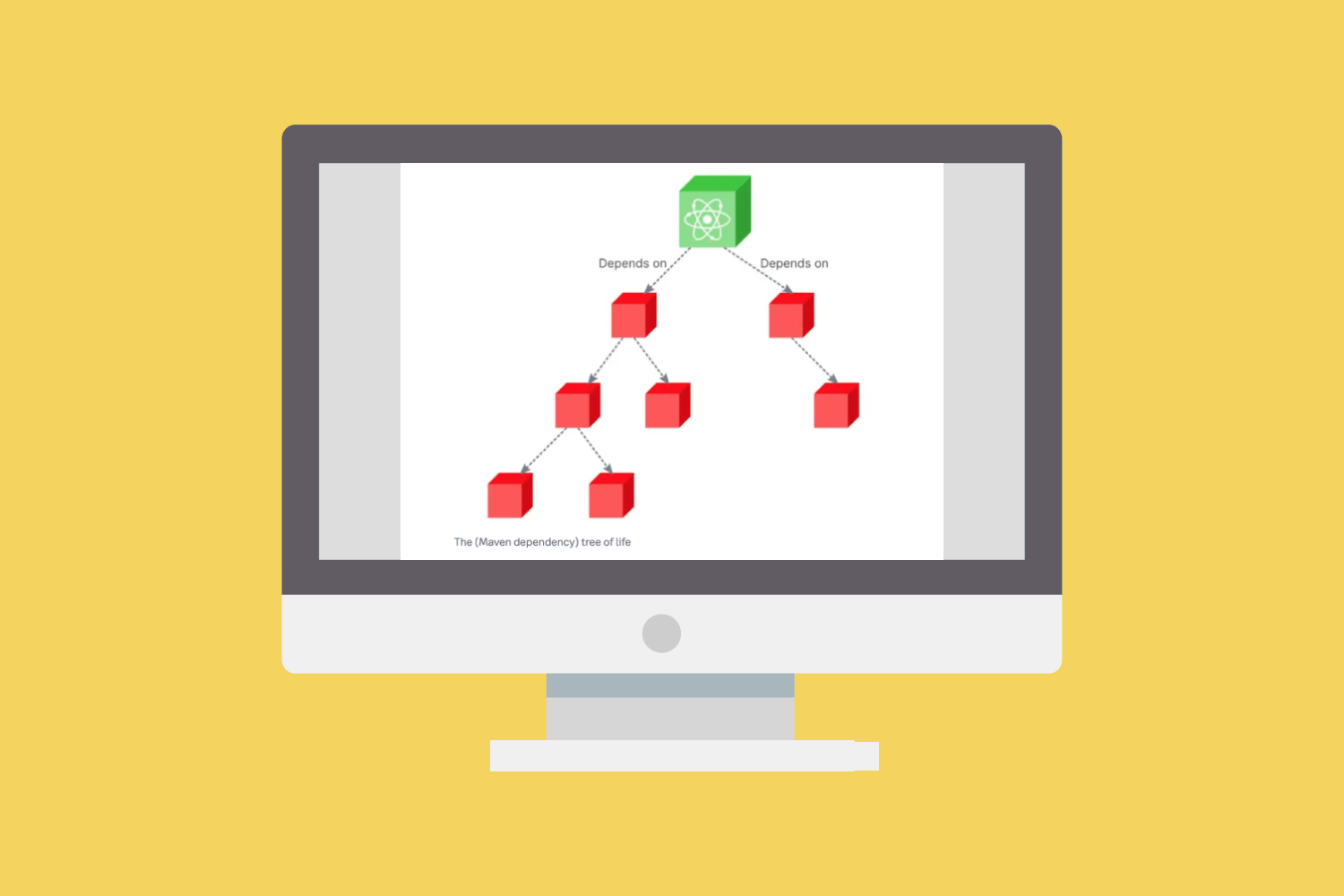
VulnerableCode is a free and open database of FOSS package vulnerabilities, aggregating data across data sources. This includes NVD data, security advisories published by Linux and BSD distributions, application software package managers and package repositories, FOSS projects, GitHub and more. While focused on specific ecosystems, the aggregated data in a single database enables querying a richer graph of relations between multiple versions of a package. This specificity increases the accuracy and validity of the data as the same version of an upstream package across different ecosystems may or may not be vulnerable to the same vulnerability. We are also actively developing a prototype to discover new correlations between vulnerabilities and software packages from mining the graph.
Using a standardized package identifier, Package URL (PURL), organizes vulnerability data across data sources. Using a PURL can reliably identify, locate, and provision software packages across different tools, programming languages, package managers, packaging conventions, APIs, and databases. This replaces the complexity of differing conventions and protocols for each individual package manager, platform, type, and ecosystem with a universal and uniform approach. PURL is already adopted by OWASP, ORT, CycloneDX, SPDX, ScanCode and more – it is also being evaluated by the US NTIA as a replacement for CPE.
Automating the search and identification of FOSS security vulnerabilities is a key component of VulnerableCode. By leveraging PURLs, VulnerableCode supports decentralized data re-creation with any tool that can detect and report FOSS packages. This includes:
- ScanCodeTM Toolkit for scanning package manifest files
- DejaCodeTM for automatically checking all product packages for vulnerabilities
- Other options like ORT and OWASP tools
Watch Philippe Ombredanne, nexB’s co-founder and CTO, share a technical deep dive into VulnerableCode along with a live demo:
Getting started with VulnerableCode
VulnerableCode is part of AboutCode, a community of open source developers making open source easier to use with open source tools for Software Composition Analysis (SCA). We maintain many open source projects on GitHub including applications like ScanCode.io, tools like ScanCode Toolkit and container-inspector and emerging standards like package url.
We offer three main approaches for using VulnerableCode:
- Use VulnerableCode.io to look up vulnerabilities for a package or a list of packages (via API).
- Use DejaCode to access VulnerableCode, where you can ingest or create an SBOM and immediately see or report the corresponding package vulnerabilities for the packages. Sign up for a free account to get started.
- Download and install VulnerableCode to build your instance of a VulnerableCode database.
The AboutCode team is building more functionality and integrations, including new pipelines in ScanCode.io to report software vulnerabilities for packages identified from a Scan.